(and What to Do About it)
If your organization continues to require faxing capability, and your IT team is still supporting that need with desktop fax machines, in-house fax servers and analog fax lines, I have some bad news, some good news, and some more bad news. Which would you like first?
Let’s get some of the bad news out of the way.
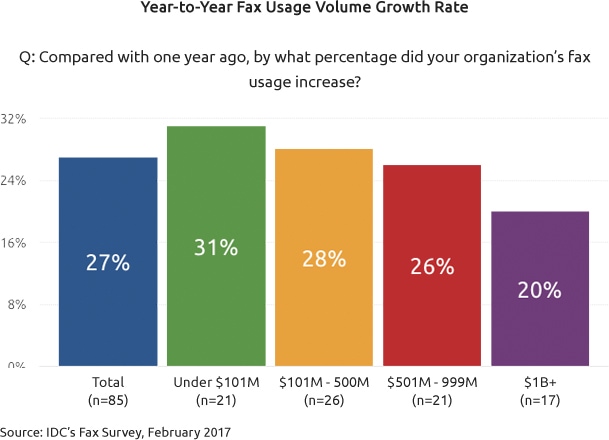
The bad news is, if your company uses fax today, the need for fax capability is probably here to stay for a while. When IDC surveyed hundreds of organizations across several key industries — including healthcare, manufacturing and financial services — they found that all of these industries were experiencing an increase in fax usage year over year.
When they asked these businesses why this was so, why they were still supporting a legacy communication protocol and even using it more frequently year over year, the most common response the researchers received was that “Customers and suppliers use it, which forces us to use it.”
Which means whatever troubles you and your IT team have propping up your in-house fax infrastructure — fax machine paper jams, crashed fax-server hard drives, etc. — aren’t going away anytime soon.
The Good News: A Unencrypted Analog Fax Might Be More Difficult to Hack Than an Unencrypted Email
The good news, however, is that although maintaining your legacy fax infrastructure might be costly and time-consuming, in one way it can give your company a security advantage over sending the same confidential or proprietary data as an unencrypted email.
Indeed, because the typical analog fax traverses the Public Switched Telephone Network, and even though it is not encrypted, it is still difficult to hack while in transit. Whereas an email is sent as plain text — easily intercepted and read or altered if it’s traveling over the Internet without the benefit of encryption — a standard fax is transmitted essentially as a voice call, although the a hacker would need some sophisticated fax-decoding technology to grab the data in transit. And to do that they would need physical access to a secure telephone company central office, or direct access to the right pair of copper phone wires leaving your office.
So if you and your IT team are still maintaining an infrastructure of old fax hardware connected to legacy phone lines, that’s your one bit of good news: It’s almost certainly more secure, and as a result probably more likely to comply with your industry’s data-privacy regulations, than unencrypted email, which should never be used to transmit information about your customers.
The Bad News: There Are Plenty of Ways Your Company’s Fax Processes Might Be Violating Data Privacy Law Right Now
But here’s a lot of other bad news — and it’s serious. If your team is continuing to prop up aging in-house fax hardware like fax machines, fax-enabled multifunction printers and onsite fax servers, your staff could be unknowingly violating your industry’s data privacy laws — HIPAA, GLBA, SOX, FERPA, etc. — every day.
Here are five possible ways your company could be in noncompliance without even knowing it.
1. Your staff leaves paper faxes containing personal customer data in public areas
This is probably the easiest way to land on the wrong side of any of the major federal laws protecting customers’ personally identifiable information (PII).
No matter how secure your fax transmissions are, if an inbound or outbound fax containing PII sits unattended on a fax machine in your office, particularly if the fax machine is located in a common area where other employees or even visitors might see it, this could be deemed a compliance violation.
Because all of these privacy laws — HIPAA, SOX, etc. and their state level equivalents — demand that businesses who handle PII maintain a tight chain of custody on this data at all times, you have to assume that if federal (or state) auditors were to visit your organization and ask to review how you transmit PII via fax, they would probably view this part of your process as a red flag.
2. Your fax records retention processes fall short of compliance.
The major data privacy laws all have requirements for retaining records that contain PII —for example, that such records be maintained for some number of years, that they are stored securely at all times, and that they’re accessible if regulatory auditors ask to review them.
One of the problems with using paper-based faxing to send and receive PII data is that this type of faxing is largely a de-centralized process that the organization’s IT team or other administrators can’t fully track or document.
If someone in one of your company’s office receives a fax containing personal data about your customers — in other words, a fax regulated under your industry’s privacy laws — what’s your IT team’s process for ensuring you receive a copy of that fax and any relevant metadata about the transaction, so you can log it and secure it for record-keeping purposes? How would you even know that the transmission took place?
There are plenty of ways your company’s faxing processes might be violating data privacy laws right now.
3. The hard drives of your fax machines and multifunction printers contain records of transmitted PII — another reason these devices are a security weakness.
Many organizations miss this faxing compliance vulnerability, so take note of it now. The desktop fax machines and multifunction printers your employees use to send and receive faxes actually store records of those faxes on their hard drives — and these records stay there until they are written over by new fax data.
This means that if your staff is transmitting PII data through your fax hardware, the drives of that hardware become a weakness in your data security process. To bring the devices up to compliance levels, you would need to secure their hard drives, implement a process for frequently wiping the data from them, or find some other way to tighten up this weak link in your regulated data’s chain of custody.
And if you’re thinking this sort of oversight would never come to the attention of federal regulators, consider this news item reported in the healthcare publication 4MedApproved. HIPAA auditors fined one health provider $1.2 million for returning leased copy machines that still had patient records on their hard drives.
It can happen. You’ve been warned.
4. Purging your fax servers’ hard drives creates another compliance vulnerability.
Let’s assume the in-house fax servers your IT team manages have secured hard drives. (If they don’t, the drives themselves are another security and compliance weakness in your fax infrastructure.)
Even though the digital copies of your faxes, which are stored as image files, can be considered secure as long as they’re on the fax servers’ hard drives, eventually these drives reach capacity and have to be purged to make room for the records of new fax transmissions.
Often in these situations, someone in the organization will be tasked with printing out the contents of the drive so the archived faxes can be filed away for auditing and record-keeping purposes.
But here again, we have a chain-of-custody issue for any of those faxes that contain PII or other regulated data. Someone not authorized to view this personal customer information could walk by and see it. Someone might mistakenly leave these pages in an open and accessible area of the office.
Unless you have implemented a secure method of purging, printing and scanning and filing all fax records from your servers — a process that includes a tight chain of custody around both the digital and hardcopy versions of the records your company is purging — you should assume this part of your fax infrastructure also fails to meet data privacy compliance.
5. Your company lacks a documented process for securing faxed PII — which itself is probably a compliance violation.
Finally, it’s important to understand that one thing all major data privacy laws — HIPAA, GLBA, SOX, FERPA, etc. — have in common is a requirement that regulated businesses develop and maintain a documented process detailing how they secure and safeguard the personal customer data under their care.
As a company in a regulated industry, you are obligated not only to secure your customers’ personal information — you’re also obligated to document how you do it, and to have that documentation handy if compliance auditors ask to review it.
And although your business may well have this documentation detailing how you protect PII on your servers, in your email network and through your cloud service providers, I’m guessing you haven’t yet documented a step-by-step description of how your team fortifies your faxing processes or secures your archived fax data after you’ve sent or received it.
For these and other reasons, your existing fax infrastructure likely falls short of compliance in at least a few ways. And unfortunately, if you maintain these legacy fax processes, you will find it difficult to bring the entire process up to your regulator’s standards.

Bring All of Your Fax Processes Up to Compliance — Migrate to a Cloud Fax Partner Like eFax Corporate
But you can solve all of the compliance issues I’ve discussed here by making one simple migration — to a fully hosted cloud fax service like eFax Corporate.
For two decades, our enterprise-caliber service has been helping businesses in the most highly regulated industries receive, send and securely store their sensitive fax data. And today we are the cloud fax solution trusted by more regulated organizations — in healthcare, financial services, the law, real estate, manufacturing and government services — than any other provider.
With a cloud fax platform designed to meet the data transmission and storage needs of highly regulated businesses like yours, eFax Corporate knows how to deploy a custom solution that meets your firm’s needs for robust faxing capability, that helps bring your processes in line with regulators, that protects your fax data with the most advanced security available, and that will even lower your overall fax costs. Cloud-based faxes are encrypted in transit and while in storage. Every fax has a detailed audit trail, and can be stored on off-site secure cloud servers, for as long as your document retention policies allow.











